DressCode Android Botnet Still Here?

Smartphones are one of the latest technological trends recently and have contributed immensely to the disruption of businesses in and around the world. The need of always staying active on the social front and always remaining connected to the Internet, are some of the reasons that have led to the boost in the smartphone rise.
With the rise in smartphone usage, the need for mobile applications has also skyrocketed. Businesses have realized the importance of mobile applications for their success and cannot afford to be left behind in the mobile apps race.
Android happens to be the most used and popular Operating System for the smartphones, and it is this popularity that has also affected the OS adversely. As much as Android enjoys being the center of attraction in the smartphone party, it is also attacked and misused that often.
One such threat to Android smartphones is botnets. A botnet is a group of Internet-connected devices that are held as a bunch without their users' knowledge. These are then used for performing malicious activities such as distributed denial-of-service DDoS attacks, spamming, data theft, and privacy attacks.
The practice of introducing malicious programs into Android applications has increased only recently, and companies and white hat hackers continually work towards a better future by identifying and removing these threats from the root.
In one such incident, a botnet, dubbed as DressCode, was discovered way back in September 2016. the news portals had reported back then that the software had infected about 500,000 to 2,000,000 devices and users through several Android applications.
Google had revealed that it was removing about 40 malware-infected applications from its store to get rid of the malware. DressCode is basically an Android Trojan that converts the infected devices into proxy servers.
Now, about 16 months after the discovery of the malware, it is reported to be still around. The removing of the malicious Android applications from the Play Store would have been the last straw, but that was not true. The program has increased in its scale and is very much there on the Google Play Store.
DressCode's method of attacking its infected mobile devices has not changed even one bit. The malware even today exploits the listening ports and creates open ports on Android devices. As a result, the wrongdoers can simply enter into the victim's system and steal sensitive information.
Moreover, DressCode's botnet bypasses all firewalls that might be upheld by routers in homes and SMBs. Botnets have always been a pain point for security researchers and consumers. The fear is real as DressCode still lurks around to infect Android devices.
According to a hacker who has revealed that DressCode is still around, the malware could probably affect as many as four million devices today. Recently in October 2017, Symantec also revealed the presence of a new batch of malicious Google Play apps that have been downloaded about 2.6 million times. Symantec likes to call this new malware Sockbot, which uses the C2 server just like DressCode did, and also exploits freely available, unauthenticated programming interfaces as DressCode did, for the purpose of click frauds.
What steps Google took to take down the malicious software are not clear. In a process called sinkholing, generally, the security companies, or the affected software application development companies are known to seize control of the Internet domains that are used to run botnets.
As these vulnerabilities are exposed, we are also exposed to the threats of being technologically advanced and the risks that we run as a society.
While there is no list of mobile apps that are currently affected by DressCode, it becomes extremely important to not install applications that seem fishy. A thorough research on the company that has uploaded any mobile app, and on its developers can result in a better security.
Similar Articles
The printed circuit board industry is undergoing one of the most transformative periods in its history
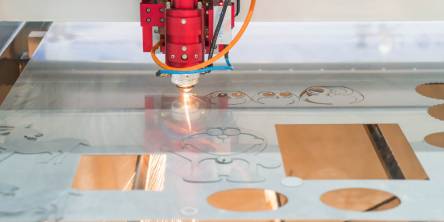
Laser marking systems have emerged as an essential tool for modern manufacturing processes, driving efficiency and enhancing production throughput. As industries adopt Industry 4.0 technologies, the need for faster, more accurate, and more reliable marking solutions becomes increasingly important.
Discover why steel components are vital for durable construction—offering strength, longevity, flexibility, and reliability in modern building projects.
In modern manufacturing, the difference between a brand’s success and a costly recall often comes down to a few Newton-meters.
When you see a steel ship in the harbor, the first impression is usually sheer scale.
Explore CNC turning—its components, process, benefits, applications, and future trends shaping modern precision manufacturing in various industries.
In the competitive industry of car manufacturing, attaining exceptional performance along with an innovative design needs the incorporation of modern manufacturing technologies
Facing delays, quality issues, or supply chain problems in hardware manufacturing? Learn the top 7 challenges—and practical fixes—to streamline production.
In the rapidly advancing landscape of high-tech manufacturing, electronics, and materials science, diamonds are no longer just gemstones they’re high-performance materials redefining what’s possible in technology.